Support this post with a reaction:
The various layers of the OSI model are explained Below
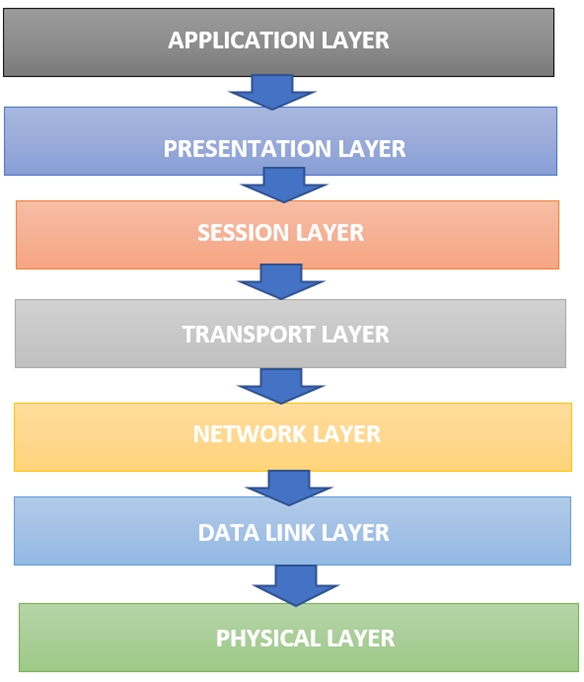
1. Application layer
- The application layer is the uppermost layer of the OSI model.
- The application layer is used by network applications like computer applications like chrome, firefox, outlook, skype etc.
- This layer involves various protocols like HTTP, SMTP, HTTPs and FTP. That protocol allows the transmission of web document requests, email messages and transfer of files between two end systems.
- The protocols of application layers provide the basic network services like file transfer (FTP is used), web surfing (HTTPs is used), emails (SMTP is used), virtual terminals (Telnet is used) etc.
- The internet application layer serves as a window for the application services to access the network.
2. Presentation layer
- The presentation layer receives data present in the form of characters and numbers from the application layer.
- The presentation layer converts the received data in machine language, which is in binary format. That’s why this is known as the translation layer.
- The main functions of this layer are data translation, data compression and data encryption or decryption.
- This layer gives services that permit connecting applications to interpret the meaning of the data exchange.
3. Session layer
- The session layer helps to set up and manage connections and enables sending or receiving data, followed by termination of corrections or sessions.
- The session layer is reliable for installing connection, authentication, and assurance of security.
- The session layer helps in session management, authentication and authorization.
- Dialog controller is the other function of this layer that permits two devices to start a connection with each other in half and full duplex.
4.Transport layer
- This layer controls communication reliability to segmentation, flow control and error control.
- The transport layer is responsible for the end-to-end delivery of the whole message.
- This layer gives the acceptance of the successful data transmission and re-transfer the data when any fault is found.
- The protocols of this layer are TCP (Transmission control protocol) and UDP (User datagram protocol).
- The services allowed by the transport layers are connection-oriented services: this service includes three phases operation- connection establishment, data transmission and termination.
5. Network layer
- The transport layer passes the data segments to the network layer. The network layer works to transmit the received segments from one device to another device positioned in different networks.
- Functions of the network layer are logical addressing, routing and path determination.
- The network layer involves the IP protocol, which explains the fields in the network layer protocols and how routers act on these fields.
- The network layer is reliable for datagrams (network layer packets) to transmit from one host to another host.
6. Data link layer
- Data link layer receives packets (datagrams) from the network layer.
- This layer is divided into two sublayers i.e., logical link control and media access control layers.
- The data link layer adds the MAC address of the receiver and sender in the header of every frame.
- The data link layer permits to define a protocol so that two or more devices can establish a connection or terminate a connection.
- It determines a particular data format over the network to establish reliable and efficient communication between two or more devices.
7. Physical layer
- The physical layer is the lowest layer of the OSI model.
- After receiving the bits from the transport layer, network layer and data link layer physical layer converts it into signals and transmit all over the media.
- These signals can be electrical signals (in LAN cable) and radio signals (in AIR).
- This layer determines the type of encryption (i.e., how the 0s and 1s are encrypted in a signal) and this layer is also trustworthy for the connection of the unstructured new data flows over an actual medium.
